最佳答案
The concept of a computer firewall has undergone significant transformations since its inception. The evolution of this technology has been marked by a series of innovations, each building upon the previous one. In this response, we will delve into the design of computer firewalls, exploring their origins, functions, and the various layers that comprise them.
The concept of firewalls dates back to the early days of computer networking. In the 1980s, as the Internet began to take shape, the need for a secure and controlled environment for communication arose. This led to the development of the first firewalls, which were primarily used to segregate networks and restrict access to certain resources.
In the early days, firewalls were simply a set of rules implemented on routers or gateways to control incoming and outgoing network traffic. These early firewalls were relatively simple, relying on basic filtering mechanisms to block or allow traffic based on certain criteria such as IP addresses, ports, and protocols.
As the Internet grew and the need for increased security became more pressing, firewalls evolved to incorporate advanced features. One such significant advancement was the introduction of stateful inspection firewalls. These firewalls maintained a record of ongoing connections, allowing them to **yze the context in which requests were being made, rather than just examining the packet headers. This enabled more accurate and effective filtering of traffic.
The next major breakthrough in firewall technology came with the introduction of intrusion detection and prevention systems (IDS/IPS). These systems used machine learning algorithms and statistical **ysis to identify and block malicious traffic, including advanced threats such as malware, zero-day attacks, and denial-of-service (DoS) attacks.
Firewalls have since evolved to incorporate a wide range of features, including virtual private networks (VPNs), secure shell (SSH) access control, and network address translation (NAT). The development of cloud-based firewalls has also enabled secure connectivity and access to cloud-based services and infrastructure.
In addition to these features, modern firewalls often integrate with other security solutions, such as antivirus software, intrusion detection systems, and incident response platforms. This integration enables a comprehensive security posture, providing real-time threat detection and response capabilities.
In conclusion, the design of computer firewalls has undergone significant transformations since their inception. From simple packet filtering to advanced stateful inspection and IDS/IPS, the evolution of firewalls has been marked by a series of innovations. As the threat landscape continues to evolve, the need for robust and adaptable firewall solutions will remain, ensuring the security and integrity of computer networks.
其他答案
The design of a computer firewall is a complex process that involves multiple layers of security measures to protect a computer or network from unauthorized access and malicious attacks. The concept of a firewall dates back to the 1980s, when it was first introduced as a simple network access control system. Since then, firewalls have evolved significantly, incorporating advanced technologies and features to provide robust security.
At the foundation of a computer firewall is the operating system (OS). The OS serves as the backbone of the firewall, providing the necessary infrastructure for the firewall to function. The OS is responsible for managing system resources, handling network connections, and executing firewall policies. Modern operating systems, such as Windows, macOS, and Linux, all have built-in firewall capabilities.
One of the key components of a computer firewall is the network interface controller (NIC). The NIC is responsible for managing network traffic, filtering incoming and outgoing packets, and enforcing security policies. The NIC works closely with the OS to implement firewalls, providing real-time monitoring and filtering of network traffic.
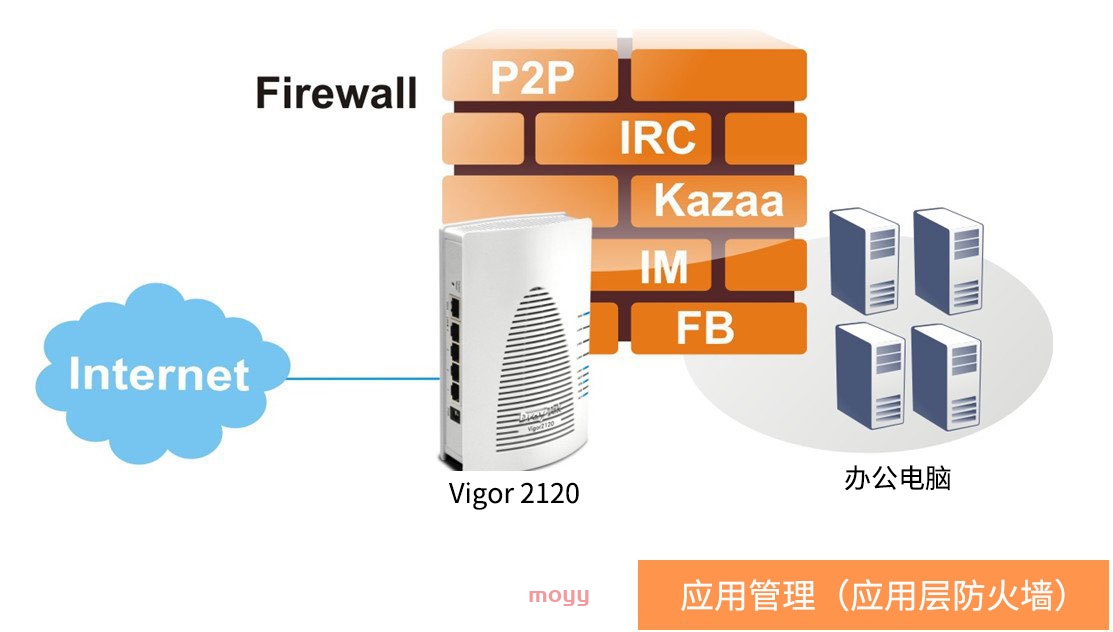
Another crucial aspect of a computer firewall is the packet filtering mechanism. Packet filtering involves examining each incoming and outgoing packet to determine whether it conforms to predetermined security rules. These rules are based on factors such as source and destination IP addresses, port numbers, and packet content. If a packet does not meet the security criteria, it is blocked or discarded.
Firewall policies, also known as access control lists (ACLs), play a vital role in the design of a computer firewall. ACLs define the rules for filtering and controlling network traffic, ensuring that only authorized traffic is allowed to pass through the firewall. These policies can be customized to meet specific security requirements, such as blocking malicious IP addresses or restricting access to sensitive areas of the network.
In addition to packet filtering and ACLs, computer firewalls also employ advanced technologies such as intrusion detection systems (IDS) and intrusion prevention systems (IPS). IDS systems monitor network traffic for signs of malicious activity, alerting administrators to potential threats. IPS systems take it a step further, actively blocking malicious traffic to prevent damage to the system.
Network address translation (NAT) is another feature of computer firewalls that enhances security. NAT allows multiple devices to share a single public IP address, making it difficult for attackers to identify and target specific devices. This feature helps to conceal the internal IP addresses of devices behind the firewall, reducing the risk of attacks.
Furthermore, computer firewalls can be configured to provide virtual private network (VPN) support. VPNs create a secure, encrypted connection between remote devices and the firewall, allowing secure access to the network. This feature is particularly important for remote workers, business partners, and customers who require secure access to the network.
In conclusion, the design of a computer firewall is a multi-layered process that involves the operating system, network interface controller, packet filtering, firewall policies, IDS/IPS, NAT, and VPN support. Each of these components plays a critical role in providing robust security for a computer or network, ensuring the protection of sensitive data and preventing unauthorized access.